Application of RFID technology in intelligent building security system
[ad_1]
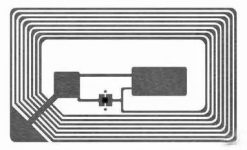
Radio Frequency IDentification (English: Radio Frequency IDentification, abbreviation: RFID) is a wireless communication technology that can identify specific targets and read and write related data through radio signals without requiring mechanical or optical contact between the identification system and specific targets. The radio signal is an electromagnetic field tuned to a radio frequency to transmit data from the tag attached to the item to automatically identify and track the item. Some tags can obtain energy from the electromagnetic field emitted by the recognizer during identification, and do not require a battery; there are also tags that have a power source and can actively emit radio waves (electromagnetic fields adjusted to radio frequencies). The label contains electronically stored information and can be identified within a few meters. Unlike the barcode, the radio frequency tag does not need to be in the line of sight of the recognizer, and can also be embedded in the tracked object.
1. The composition principle
1. The system is divided into three parts
(1) Label (Tas)
The label is equivalent to the bar code symbol in the bar code technology, used to store the information that needs to be identified and transmitted.
(2) Reader
Depending on the types of tags supported and the completed functions, the complexity of the reader is significantly different. The basic function of the reader is to provide a way for data transmission with the tag. In addition, the reader also provides quite complex signal state control, parity error checking and correction functions.
(3) Antenna
The antenna is a transmitting and receiving device that transmits data between the tag and the reader.

2. Working principle
RFID technology is a technology that uses radio frequency signals through spatial coupling (alternating magnetic field or electromagnetic field) to achieve contactless information transmission and achieve automatic identification through the transmitted information. The working principle is: the use of radio frequency signals and spatial coupling transmission characteristics to realize automatic identification of the identified objects. Working process: When the item with the electronic tag is within the readable range of the reader, the reader emits a magnetic field, the query signal will activate the tag, and the tag requires a reflection signal according to the received query signal, and the reader receives After the signal reflected by the label, the electronic data stored in the electronic label can be read and identified contactlessly through the decoding process of the internal circuit, so as to achieve the purpose of automatically identifying the object. And then further realize the collection, processing and remote transmission management functions of the object identification information through the computer and computer network.
Second, the design in Yu Security
1. Structural design
Taking into account the diversity and complexity of the road sections that the buildings and people in the community may pass through, it is necessary to install several readers and exchange them with the computer of the monitoring center through the communication line. At the same time, an electronic tag is placed on each vehicle of the personnel entering the community to monitor and locate it.
In the working process of the RFID system, energy is always the basis, and data exchange is realized through a certain time sequence. The reader provides working energy to the electronic tag. When the electronic tag enters the radio frequency identification field, the radio frequency wave emitted by the reader activates the tag circuit, interacts, and completes the data exchange. For simultaneous reading of multiple tags, either the reader or the tag can be used.
In order to realize multi-tag reading at the same time without conflict, the reader first issues isolation commands to a batch of tags, so that multiple electronic tags within the reading range of the reader are isolated, and finally only one tag is kept in an active state, and no conflict is established with the reader. Communication link. For the tag-first approach, the tag randomly sends its own identification ID repeatedly, and different tags can be correctly read by the reader at different time periods, and multiple tags can be read at the same time. For any electronic tag, it has a unique ID number. In most applications, the data attributes of the tag are supported by the use of a back-end database. The interface between the reader and the application system is represented by a standard function called by the development tool. The function roughly includes the following aspects: the application system issues configuration commands and other instructions to the reader as needed; the reader returns its current configuration status and the execution results of various instructions to the application system.

2. Work process
Each vehicle entering the community must wear an identity card (including personnel card and vehicle card) issued by the security guard-radio frequency identification tag when passing through the gates of the community. Its chip contains a unique identification code and a user-specified code. Information, they can be read out by a reader in a non-contact manner within a certain distance. The dynamic monitoring system based on radio frequency identification technology can simultaneously track and identify multiple target objects with radio frequency tags within a certain range without contact, high speed and accuracy, so only place radio frequency identification tags on people and vehicles entering the community (Usually it is packaged as a card, so it is also called a radio frequency card). When the personnel and vehicles entering the community drive within the effective reading range of the reader, the reader of the system will automatically read the radio frequency held by the personnel and vehicles Identify the ID number of the tag, and then the system will transmit the ID number of this tag and related information about the driving of personnel and vehicles to the background system for processing.

Third, the application in the security system
1. Functional design
The basic functions realized by RFID technology in personnel location management include:
①Recognition: How many people or vehicles are there at any time or in a certain place, and who can fully identify these people or vehicles;
②Recording: the activity trajectory of all people and vehicles entering the community at any time in the community can be recorded in the database;
③Positioning: The community monitoring center can remotely monitor people and vehicles entering the community;
④ Inquire about a series of information such as the arrival/departure time and total stay time of relevant personnel and vehicles at any location, so as to supervise and confirm whether important inspection personnel conduct various data testing and processing on time and at the point, and fundamentally eliminate the cause Related safety issues caused by negligence.
⑤ Anti-cheating: The monitoring center can automatically recognize the identity card that the personnel and vehicles entering the community lose or discard during driving.
2. Design plan
Install several readers in the various passages of the community and the passages through which people may pass, and exchange them with the computer of the ground monitoring center through the communication line. At the same time, an RFID electronic tag identity card is placed on each vehicle entering the community. When a vehicle enters the community, as long as it passes or approaches any reader placed in the passage, the reader will sense the signal and upload it immediately. On the computer in the monitoring center, the computer can determine the specific information (such as: who, where, and the specific time), and the manager can also click on any location in the community according to the distribution diagram on the big screen or on the computer. The computer will then count and display the personnel in this area.
At the same time, once an accident occurs in the community (such as: fire, robbery, etc.), the personnel and vehicles around the accident site can be found immediately based on the personnel location distribution information in the computer, and then the detector can be used to further determine the accurate location of the personnel at the accident site , In order to help the public security department to rescue people in distress and solve cases in an accurate and quick manner.
3. The system is complete
The information processing system is the core of the entire community security system, consisting of a database system and a corresponding application software system. The system can complete functions such as recording, querying and processing related information on the driving path of personnel and vehicles. For example, it can query the driving path information of the personnel and vehicles that entered the community on March 1513, 2007.
[ad_2]